3 OTP Bots Dominating the Carding Scene — Real-Time 2FA Bypass Machines (Weekly, Monthly, Lifetime Models)
Two-factor authentication (2FA) was meant to be that unbreakable barrier against account takeovers. For a hot minute, it actually held up pretty well. Then the OTP bots showed up and changed everything in the underground game.
These aren’t your classic brute-force or exploit tools. They’re psychological automation weapons designed to trick the victim into handing over the exact code the bank or platform just texted them — in real time. In carding circles, especially high-volume financial fraud, credential-stuffing runs, and phishing kits, OTP bots have become essential infrastructure. They turn a stolen username/password combo into instant cashout access by socially engineering the second factor.
In this deep dive, we’ll expose the three dominant OTP bot models ruling the scene right now: the cheap weekly rentals for quick hits, the monthly pro setups for scaled campaigns, and the elite lifetime ecosystems that operate like private fraud factories. We’ll break down exactly how each one operates, why they’re so damn effective in 2026, and — if you’re trying to lock things down — the practical ways to shut them out. 3 OTP Bots Dominating are Weekly, Monthly and Lifetime BOTs and you can get it from Worlddumps.com.

What Exactly Is an OTP Bot in Carding Terms?
Straight up: an OTP bot is an automated voice/SMS system that calls or texts your target, pretends to be their bank, PayPal, Coinbase, crypto exchange, or whatever service just triggered the 2FA prompt, and pressures them into reading back the code. No encryption cracking, no zero-days — pure real-time social engineering at machine speed.
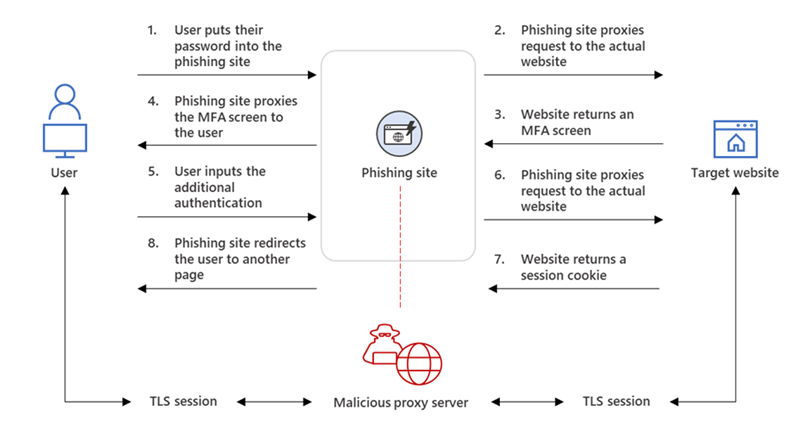
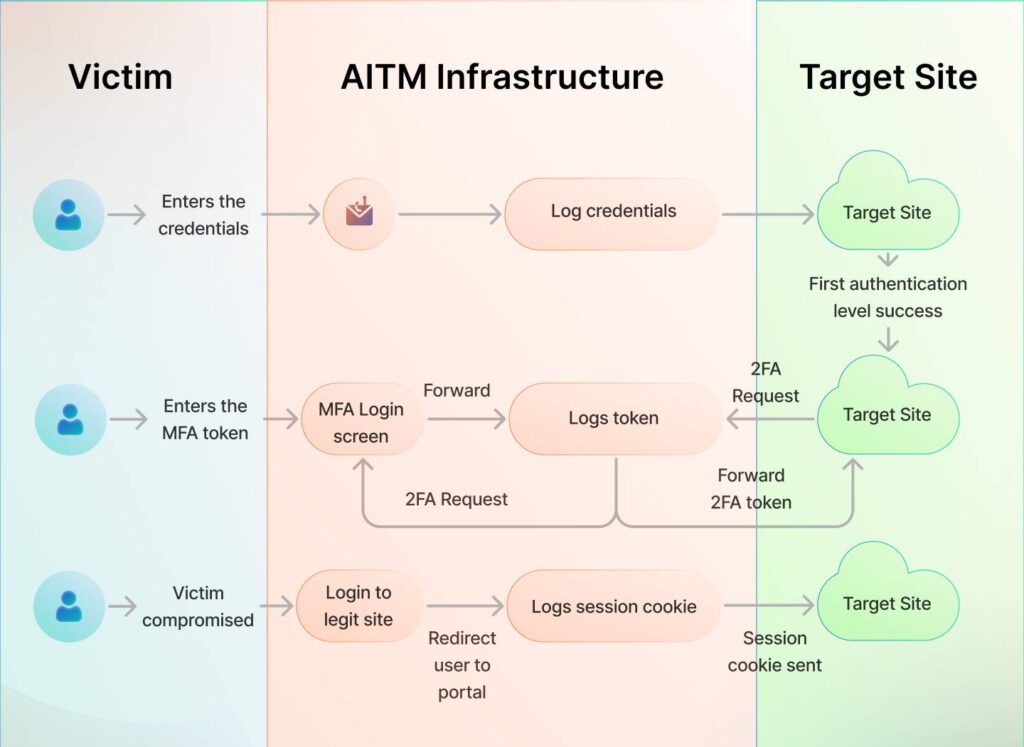
Typical attack chain in carding:
- Grab creds via phishing page, combo lists, infostealer logs, or breaches.
- Plug them into the real login endpoint (often via automated checkers or ATO scripts).
- 2FA SMS/voice prompt fires.
- OTP bot instantly hits the victim’s phone with urgency: “Suspicious login detected — verify now or your account locks.”
- Victim reads the code → bot relays it → attacker logs in and drains/mules/cashes out.
It’s not hacking the protocol. It’s hacking the human panic response, automated and scaled.
1. The Weekly Subscription OTP Bot — Entry-Level Speed Runs
These are the starter-pack bots you see advertised everywhere in Telegram channels, Russian forums, and private discords. Access usually runs $80–$200 for 7 days, sometimes you may be looking at the wrong sides World dumps OTP Weekly BOT sales for $380 and very effective. You can Buy Weekly OTP BOT Here
Core Features You Get:
- Web or Telegram dashboard for number input and mode selection
- Spoofed caller ID (bank-looking numbers, toll-free spoofs)
- Pre-built voice scripts for major targets (Chase, Revolut, Binance, PayPal, Cash App)
- Real-time OTP relay (shows up in dashboard seconds after victim enters)
- SMS fallback + voice call options
- Basic API hooks for phishing kit integration
- Voicemail detection bypass (leaves message if no answer)
How a Typical Weekly Run Goes Down: The attacker loads fresh combos, runs them through the checker, hits live logins, and the bot auto-dials the victim while pretending to be the “Fraud Prevention Team.” Script says, “We blocked a $4,987 transfer to Canada. Please verify the code that was sent to ensure the security of your funds. The victim panics, enters the digits, and the code appears, resulting in an instant takeover.
Why carders love weekly models:
- Dirt cheap entry
- No long-term commitment if the batch of cards/creds is small
- Frequent script refreshes as banks update fraud wording
- Perfect for testing new phishing domains or mule accounts
- Low risk—if OPSEC fails, just burn the sub and grab another

2. The Monthly “Pro” OTP Bot Infrastructure—Scaled Carding Ops
Step up to $950/month from World dumps OTP BOT Shop and you enter pro territory. These are full-stack fraud panels, often sold as “MFA Bypass as a Service” or bundled with ATO/checker suites.
Advanced Capabilities:
- Multi-threaded calling (hit 50+ victims simultaneously)
- Multi-language AI voices (English, Spanish, French, Arabic scripts)
- CRM-style victim tracking (response time, success rate, hang-up reasons)
- Integration with bulk SMS gateways + voice providers
- Custom script builder + interactive IVR (press 1 to confirm)
- Regional spoofing pools (local numbers per country)
- Analytics: time-to-code, failure patterns, device/OS fingerprints logged
- Often paired with SIM-swap coordinators or number rental services
Attack Flow Example (Under 2 Minutes):
- Spear-phish high-value target → credential harvest
- Attempt login on real site → 2FA triggers
- Bot calls within 5–10 seconds: “This is security — unusual activity from new device. Enter code now.”
- Victim complies → takeover → carding crew moves funds to mixer or mule wallet
These monthly beasts allow parallel campaigns across thousands of targets, region-locked attacks, and data-driven optimization. Some even log behavioral patterns to refine future scripts.
Why they’re deadly in carding: Scale + speed = higher success percentage on premium accounts (crypto, banking, high-limit cards).
3. The Lifetime OTP Bot Ecosystem—Elite Fraud Factories
Pay $2700 on World Dumps OTP Shop once (or subscription tiers up to $1k/month) for “lifetime” access — though “lifetime” usually means as long as the seller stays online and doesn’t exit-scam. These are private, heavily guarded infrastructures run by serious crews.
What You Really Get:
- Custom AI-generated voices (cloned bank reps using ElevenLabs-style tech)
- Real hold music ripped from target institutions
- Interactive voice response (IVR) with keypad simulation
- Human fallback operators (if bot fails, live person jumps in)
- Global dedicated spoofing infrastructure (thousands of clean numbers)
- Encrypted C2 channels + self-hosted panels
- Deep integration with phishing-as-a-service (PaaS), infostealer logs, and breach feeds
- Advanced evasion: detect carrier spam filters, rotate voices/scripts hourly
At this level, it’s layered attacks: SIM-swap first → intercept SMS → bot reinforces with voice → full account control. Some include malware for SMS forwarding.
Why lifetime models dominate high-end carding:
- Constant private updates (new bank scripts before public detection)
- Restricted access keeps competition low
- Precision targeting (VIP lists, whale accounts)
- Built-in money laundering hooks (crypto mixers, cashout automation)
Why OTP Bots Keep Winning in 2026
Timing is the killer feature. The bot strikes the exact second the real 2FA arrives — urgency overrides suspicion. Impersonation sounds official. Automation removes human error. Panic makes people ignore every red flag.
SMS 2FA is basically a speed bump now. Carders don’t need elite skills — just good OPSEC, fresh creds, and one of these bots.
How to Actually Stop Them (Practical Defenses)
Personal Level:
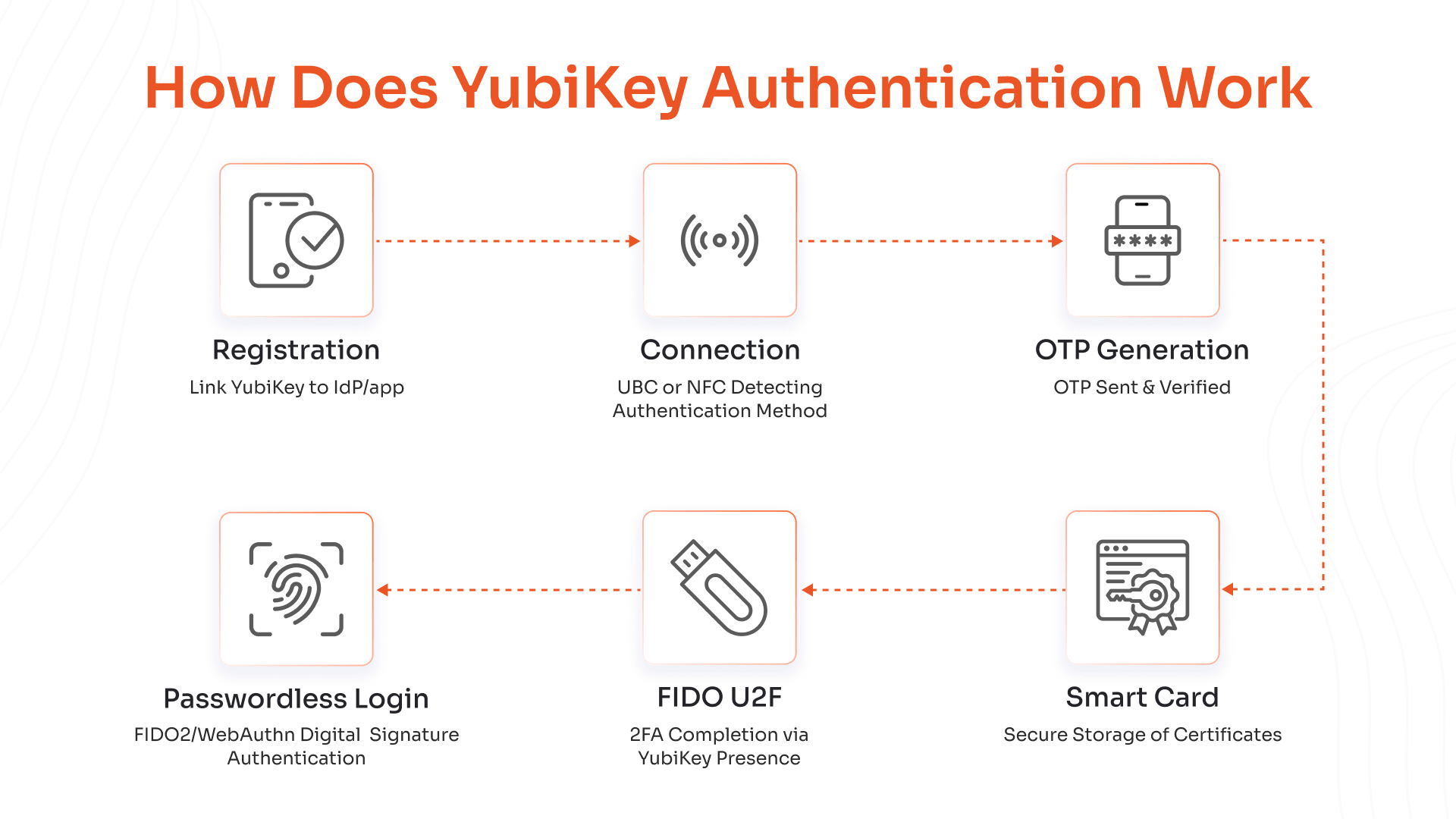
- Ditch SMS 2FA yesterday — switch to authenticator apps (TOTP), push notifications, or best: hardware security keys (YubiKey, Titan).
- Use passkeys where available (phishing-resistant by design).
- Lock SIM changes with carrier PIN or port-out freeze.
- Enable login alerts everywhere + review devices/sessions weekly.
- Freeze credit reports if you’ve been in any breach.
Business/Platform Side:
- Enforce phishing-resistant MFA (FIDO2/WebAuthn, security keys mandatory for high-risk actions).
- Implement transaction signing + behavioral biometrics.
- Real-time anomaly detection (impossible login locations, velocity checks).
- Session binding + device attestation.
- AI voice phishing detection + number reputation scoring.
- Zero-trust everywhere — never trust SMS as proof.
Conclusion
OTP bots don’t crack codes — they crack people. In carding, they’re the difference between a dead combo list and six-figure cashouts. Weekly for testing, monthly for volume, lifetime for the big leagues.
If you’re still riding SMS 2FA in 2026, you’re handing attackers the keys on a silver platter. Move to hardware MFA, passkeys, and layered behavioral checks — or keep getting owned. 3 OTP Bots Dominating are Weekly, Monthly and Lifetime BOTs and you can get it from Worlddumps.com.
Stay sharp out there.
Here is an easy link to buy an OTP BOT from World Dumps Buy OTP BOT